Mitigant Threat Catalog: 61 Techniques & 12 AWS Services Added

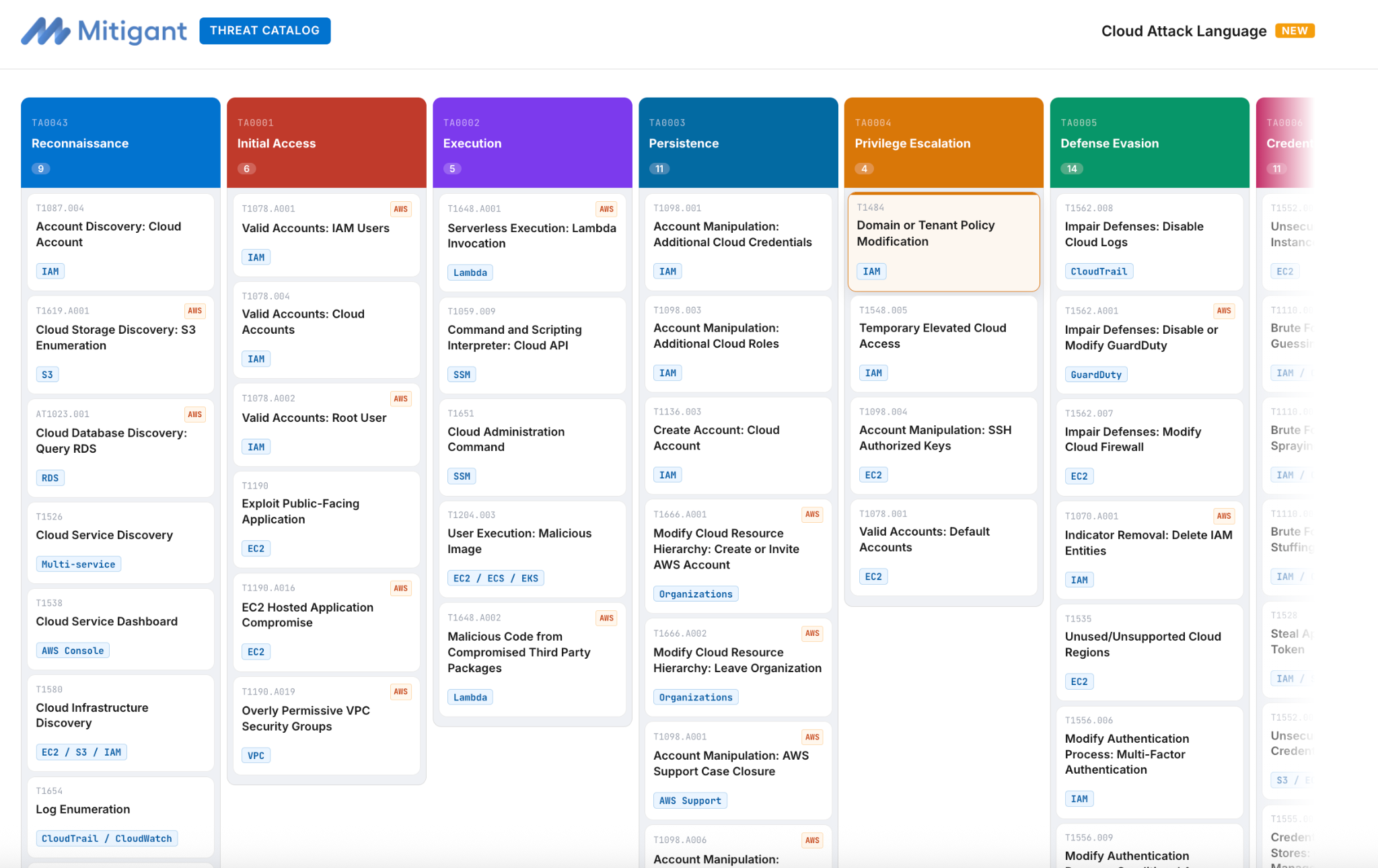
We launched the Mitigant Threat Catalog about a month ago, with a vision to close a critical gap we identified and experienced firsthand: translating knowledge described in MITRE ATT&CK from textual descriptions to operational effectiveness. The catalog launched with 30 techniques across 20 AWS services. This post discussed what has changed, the current coverage, interesting usage patterns of practitioners and feedback channels we added.
MITRE ATT&CK is deliberately abstract; it is designed as a framework for categorizing adversary behaviour, not as an operational playbook. That is not a limitation; it is the right design decision for something meant to be universally applicable. However, practitioners face a critical knowledge translation gap: moving from a high-level technique description to the exact low-level implementation an attacker would use, the specific API call to make, and the corresponding cloud event generated, which in turn informs a detection rule of which event to catch. The Mitigant Threat Catalog provides this much-needed translation, and this release takes it further.
So more concretely, let's consider T1078 (Valid Accounts: Cloud Accounts), whether you are defending an AWS, Azure or Google Cloud account, this technique explains how adversaries leverage stolen credentials to operate under legitimate identities. Essentially, the information gives insights into the what and why , but not the how. While this information might be sufficient for some audience, practitioner trying to proactively understand these techniques from a praical standpoint would need to do some research. They'll visit the provider's documentation, in an attempt to figure out the corresponding CLI commands, API calls, eventname required for effective detection. In AWS specifically, that means drilling down to aws iam create-access-key), and the possible sequence of events before and after the command is executed. The Mitigant Threat Catalog provides the above-mentioned information easily, an operational resource that empowers defenders.
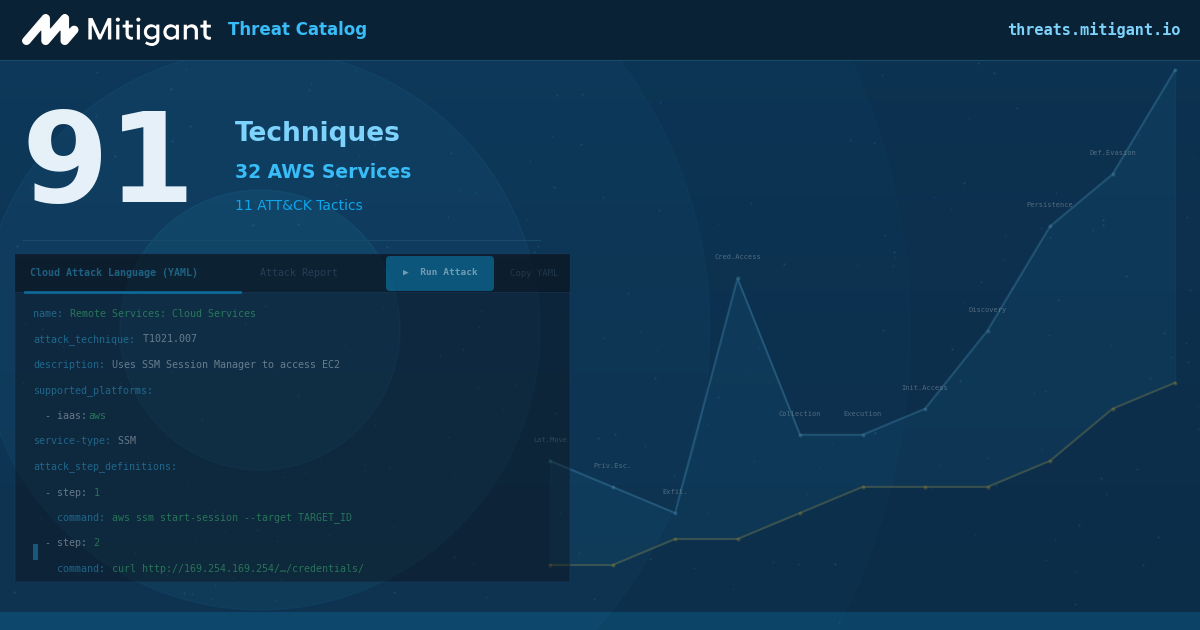
What’s New: 61 Techniques & 32 AWS Services
We have added 61 techniques and 12 AWS services, bringing the total to 91 techniques across 32 AWS services. The catalog now includes techniques across 11 MITRE ATT&CK tactics. The 12 newly added AWS services include Amazon Cognito, Amazon CloudFront, Amazon CloudWatch, Amazon DynamoDB, Amazon EventBridge, Amazon Kinesis, Amazon VPC, Amazon WorkSpaces, AWS Config, AWS IAM Identity Center, AWS Secrets Manager, and AWS Security Hub. Cognito attack techniques, in particular, are rarely documented at the operational level practitioners need. IAM Identity Center and Security Hub are high-value enterprise targets: one controls federated access across every account in an AWS organisation, the other is the detection layer attackers want to suppress first.
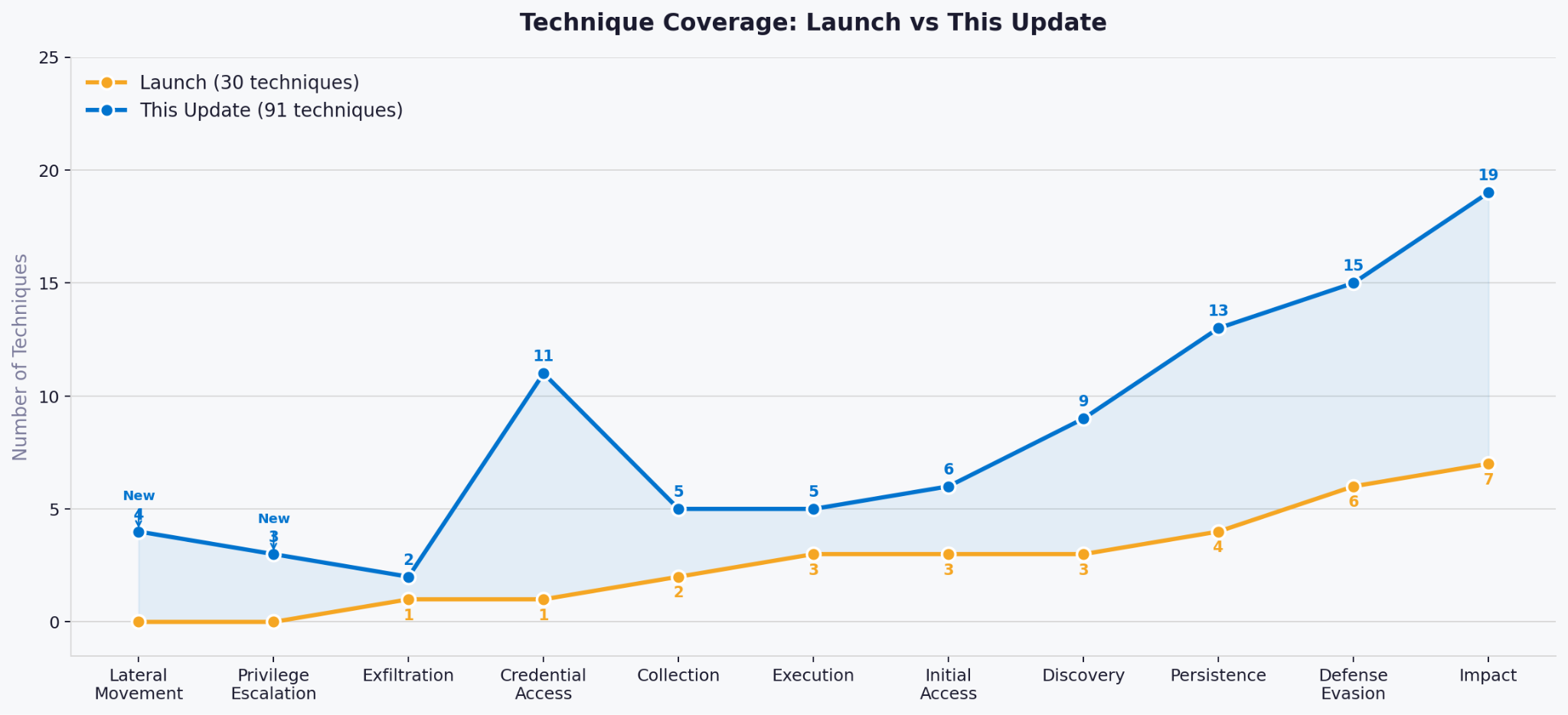
The Matrix View: Coverage at a Glance
The original card-grid interface is effective for browsing and searching for individual techniques. It does not, however, effectively communicate the shape of the catalog's coverage, especially through the lens of tactics. Understanding which tactics are deeply represented, which are thin, and how techniques distribute across the attack lifecycle requires a different interface.
The new matrix view addresses this directly, modeled after the MITRE ATT&CK matrix; it renders all 91 techniques in an 11-column tactic grid, with each column color-coded by tactic. Practitioners familiar with the ATT&CK matrix will be able to orient immediately. Each technique card shows the technique ID, title, and AWS service. Clicking any card navigates directly to the full technique detail page, with no intermediate modal or confirmation step. Both views share the same search and filter state; tactics, services, or keywords search
How Practitioners Use The Catalog
Three patterns from the first month of usage are worth sharing, not as platform metrics, but because of what they reveal about how practitioners are actually using the catalog.
Defense Against Identity-Based Attacks
The most visited techniques are all T1078 variants: Valid Accounts across IAM Users, Cloud Accounts, and the base technique. This is not surprising, IAM credential compromise is consistently the most documented initial access vector in cloud incident/threat reports, and practitioners need the executable detail to defend against it: the exact sts:AssumeRole sequences, the ConsoleLogin and GetSessionToken CloudTrail events, and the command sequences that would appear in a real compromise. The catalog gives them that directly.
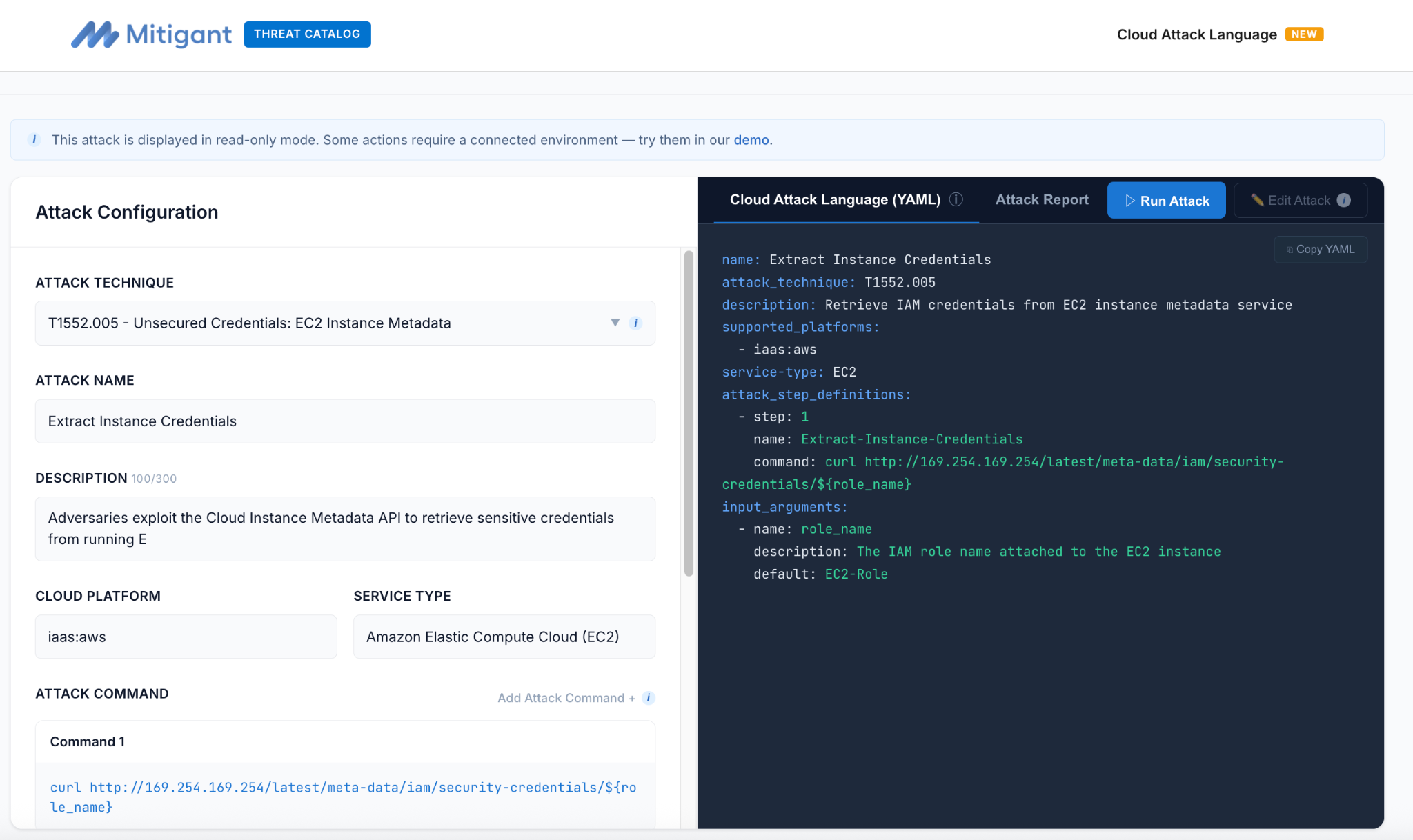
Practice over Theory: Practitioners Skip Descriptions
A large share of readers on techniques like T1552.005 (Unsecured Credentials: EC2 Instance Metadata) skip reading the descriptions and head straight to the Attack Builder . This confirms a strong preference for ‘show me the attack’ over ‘tell me about the attack’ among experienced defenders; most likely, they already know what EC2 Instance Metadata is and prefer to have a feel of what the attack technique entails e.g., curl http://169.254.169.254/latest/meta-data/iam/security-credentials/ . Funny enough, the specific command does not directly generate a CloudTrail event, making it challenging to detect.
A practitioner who goes straight to execution already knows the theory and wants to experience the action. Here is a hint: if you want to see the Attack Builder in action before connecting your own environment, the Mitigant demo provides a pre-configured AWS environment where you can run techniques without any setup.
We Want Your Feedback
Here are two feedback mechanisms many of you have been waiting for:
Suggestions/Feedback: We have added a feedback system accessible from every page in the catalog. There is a "Suggest a Technique or Report an Issue" link in the footer that opens a structured form for submitting technique suggestions, flagging corrections, or raising general feedback. When opened from a technique detail page, the technique ID is pre-populated automatically. We are anxious to hear your feedback.
Notification Signup: Since we want to keep you informed as we improve the catalog, we have introduced a means for easy information dissemination, especially for anyone who wants to be informed about new additions, including new techniques, services, or CAL scripts. T
What Comes Next
Our vision is to cover as many AWS techniques as possible; those specific to AWS, documented in the AWS Technique Threats Catalog, as well as those available at MITRE ATT&CK. We would also like to expand to other cloud service providers, e.g., Azure and Google Cloud Platform. Most importantly, we do not want to make these decisions ourselves; we look forward to suggestions and feedback that would help chart the course of the catalog such that it provides the most use.
Explore the catalog: threats.mitigant.io