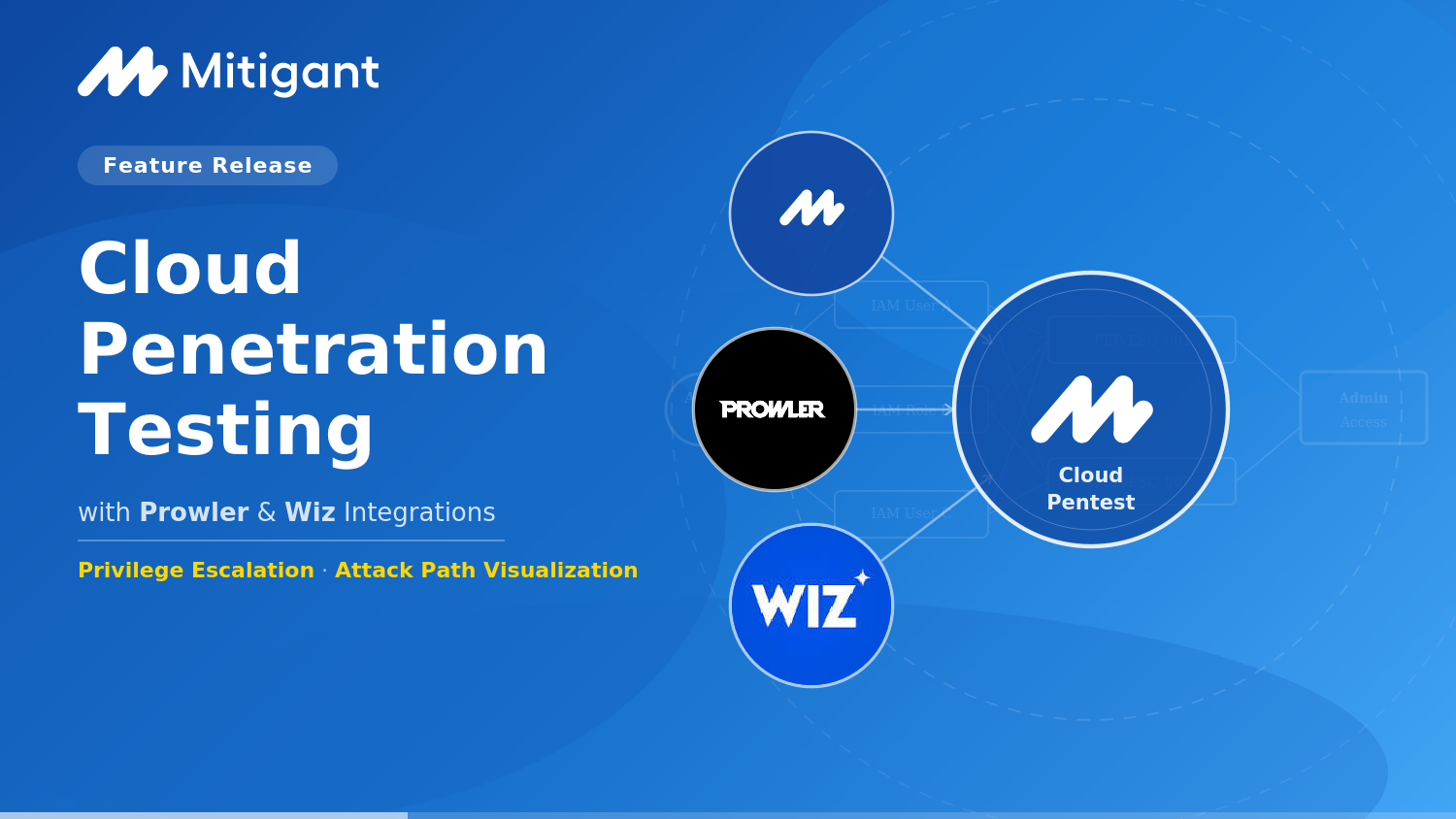
Feature Release: Cloud Penetration Testing with Prowler and Wiz Integrations

We are pleased to share a significant expansion of Mitigant's Cloud Penetration Testing , the initial release was anchored on our native Cloud Security Posture Management (CSPM). The workflow leveraged CSPM findings to drive subsequent penetration testing, including attack selection, evidence collection, and report generation. However, after discussing with customers we realized the need to support interoperability with other CSPMs already integrated in enterprise security workflows.
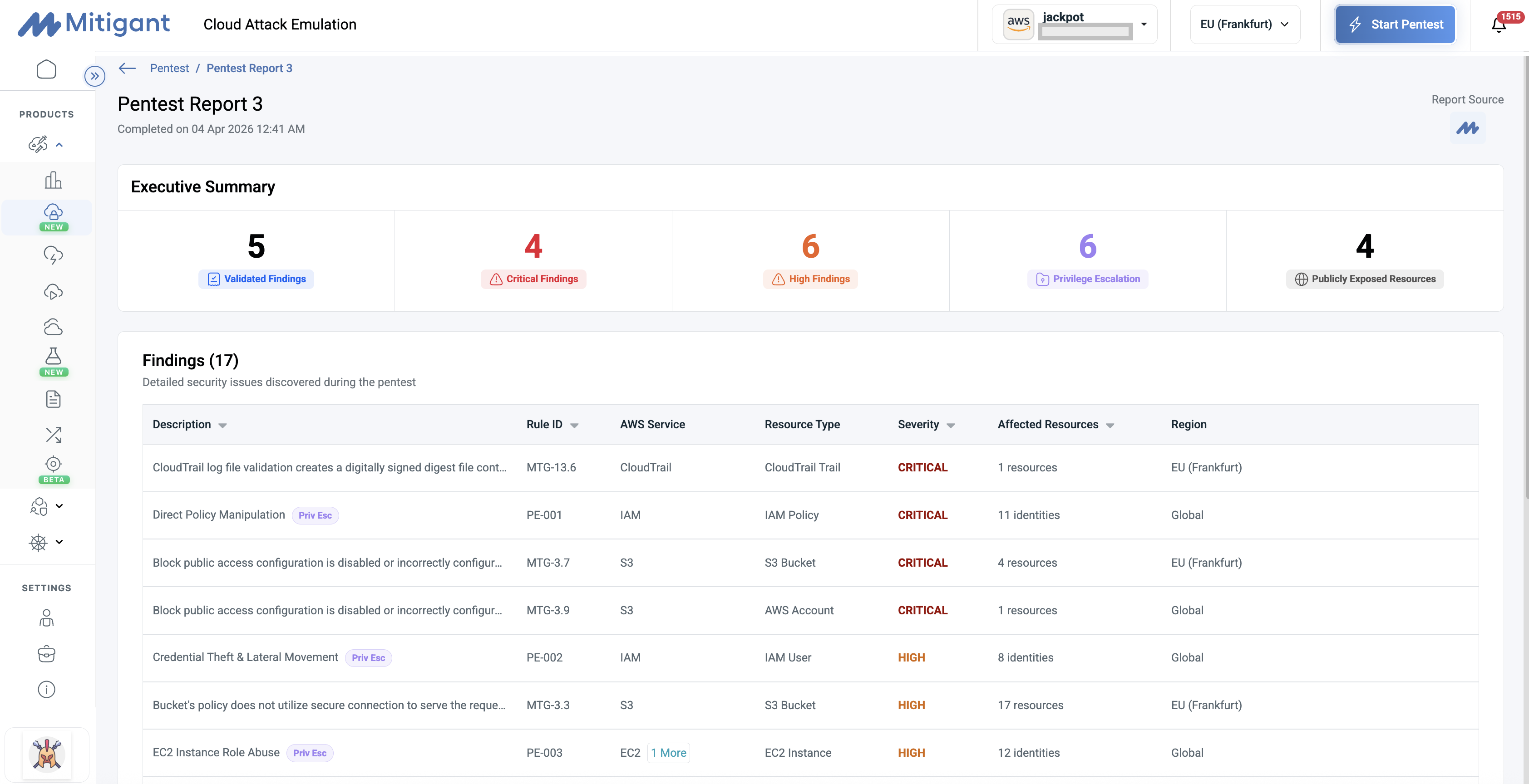
Therefore, this release adds three main capabilities: Bring Your Own CSPM support for Prowler and Wiz, Privilege Escalation, and Attack Path Visualization. The practical outcome for security teams, Managed Security Service Providers (MSSPs), consultancies already running Prowler or Wiz is significant: posture findings are automatically validated against internet-exposed resources, actual exposures, and privilege escalation paths are identified. Note that the privilege escalation paths are SCP-aware, meaning they reflect what is genuinely exploitable within AWS Organization's controls, not just what is theoretically possible. This article explores these capabilities and how they work together.
From Posture Assessment to Exploitable Findings
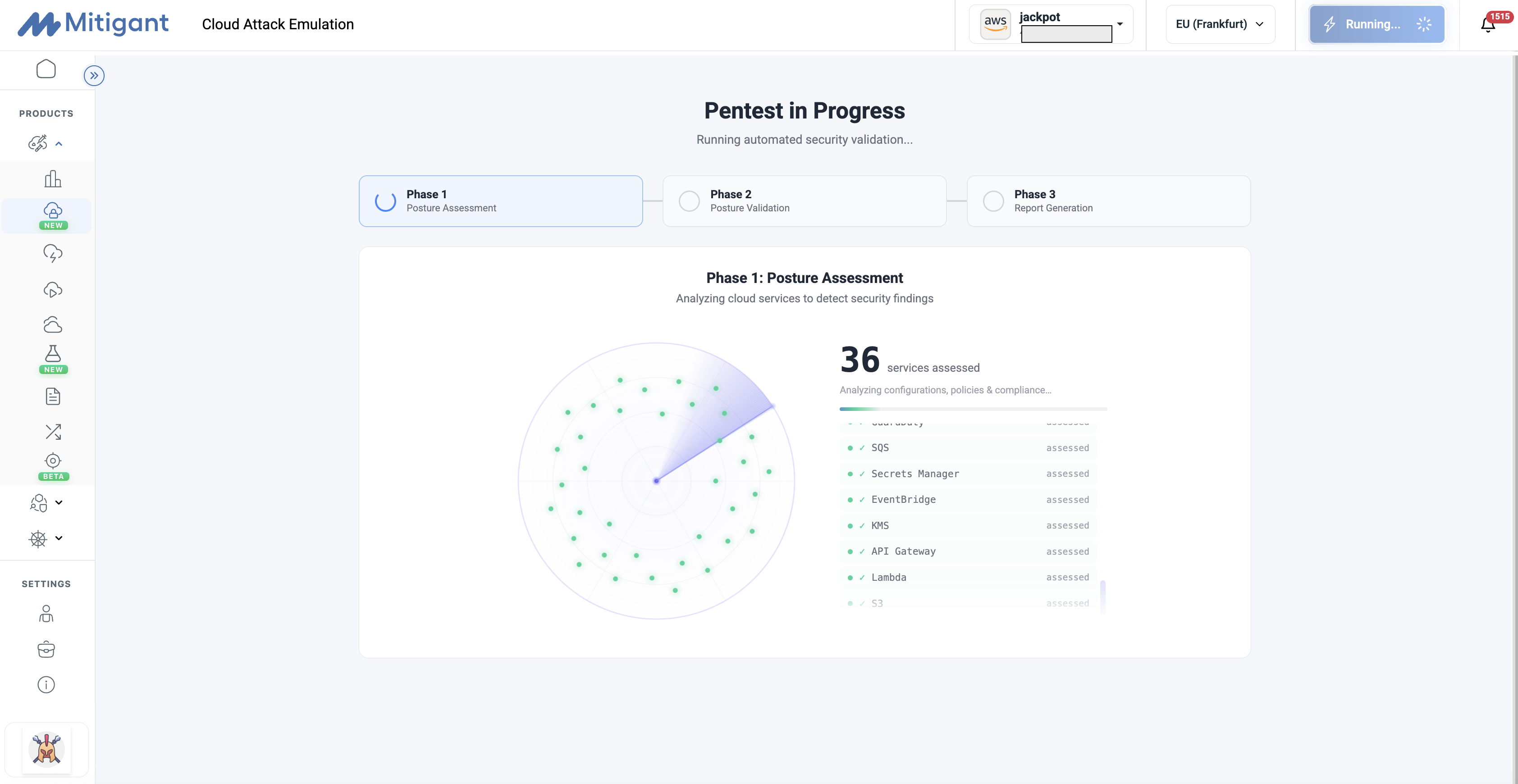
We have written before about why CSPM scans are not cloud penetration tests, the core argument: a cloud posture scan produces 2,000+ findings, most of which are noise. Without validation, security teams struggle to distinguish theoretical risks from actually exploitable ones. The outcome is alert fatigue, deprioritized remediation, and a false sense of security. Mitigant Cloud Penetration Testing addresses these challenges via a three-phase process:
Posture Assessment: The platform ingests CSPM findings, either from Mitigant's native CSPM or from imported CSPM reports e.g. Prowler and Wiz.
Posture Validation: Automated exploitability analysis narrows findings to the ~200 most actionable candidates in approximately 30 seconds. Exploitability analysis and attack emulation validate these findings by precisely testing them passively to filter out the actually exploitable ones. Optionally, users can enable the active exploitation of these filtered findings using the existing Mitigant attacks.
Exploitable Findings: The output is a set of proven threats: evidence-based, prioritized, and actionable. The noise reduction is approximately 85%.
The result is a Mean Time to Validate (MTTV) of around 5 minutes from the start of the pentest, through validation to reporting. This is the metric that matters for security teams operating under time pressure and for pentest firms that need to deliver client-ready output efficiently.
Bring Your Own CSPM: Prowler and Wiz Integrations
A significant part of the feedback we received from customers and partners was a variation of the same question: Can we run Cloud Pentests if we already use other CSPMs, such as Prowler or Wiz? The answer is now YES. The cloud pentest feature now allows uploading of third-party CSPM reports. Here are the possible options:
- Mitigant CSPM: Native, fully integrated. No upload required. The existing workflow is unchanged.
- Prowler: Import Prowler assessment reports in CSV or JSON-ASFF format and run cloud pentests.
- Wiz: Import a Wiz CSPM assessment report in CSV format and run cloud pentests.
Teams running Prowler or Wiz do not need to migrate their posture tooling to benefit from Mitigant's cloud penetration testing. Also, this integration reflects a broader mission: the accessibility of security validation as a means to focus on exploitability, especially as AI rapidly makes it easy to find security findings and vulnerabilities.
Privilege Escalation
Cloud identity is the most targeted attack surface in cloud environments. When attackers gain initial access to a cloud environment, whether through a leaked credential, a misconfigured role, or a compromised workload, their next step is almost always privilege escalation. They look for IAM users, roles, and policies that can be abused to expand access, move laterally, or gain administrative access. This pattern is consistent across the cloud breach data published by Mandiant, CrowdStrike, and others year after year. The Privilege Escalation capability validates this attack surface. It discovers real, exploitable IAM escalation paths in your AWS environment and, critically, it validates them across 28 privilege escalation techniques. These techniques span across the most commonly abused IAM primitives: policy manipulation, PassRole chains into Lambda and EC2, access key creation against high-privilege identities, trust policy exploitation, and CloudFormation-based escalation. All privilege escalation findings are mapped to MITRE ATT&CK, including T1098 (Account Manipulation) and T1562 (Impair Defenses), with cross-account paths mapping to T1199 (Trusted Relationship).
SCP-Aware Validation
One of the most common sources of false positives in privilege escalation findings is the failure to account for Service Control Policies (SCPs) configured at the AWS Organizations level. An escalation path that appears exploitable at the IAM level may be fully blocked by an SCP that restricts the relevant API calls across the entire organization.
The Privilege Escalation assessment is SCP-aware; findings are evaluated against detected SCPs to identify existing constraints. This means findings in pentest reports reflect genuinely exploitable scenarios and environments, aligned with implemented organizational controls. The practical result is a significantly lower false-positive rate than tools that evaluate IAM permissions in isolation.
Integration with the Pentest Report
Privilege escalation findings appear alongside CSPM-driven findings in the cloud pentest report, marked with a Priv Esc badge. Every finding in the report, including privilege escalation paths, is mapped to MITRE ATT&CK techniques, so security teams and pentest firms can align findings directly with the framework that underpins their detection rules, threat models, and client reports. A single pentest run captures both misconfiguration exposure and IAM escalation risk in one unified output, with evidence and MITRE mappings attached to each finding.
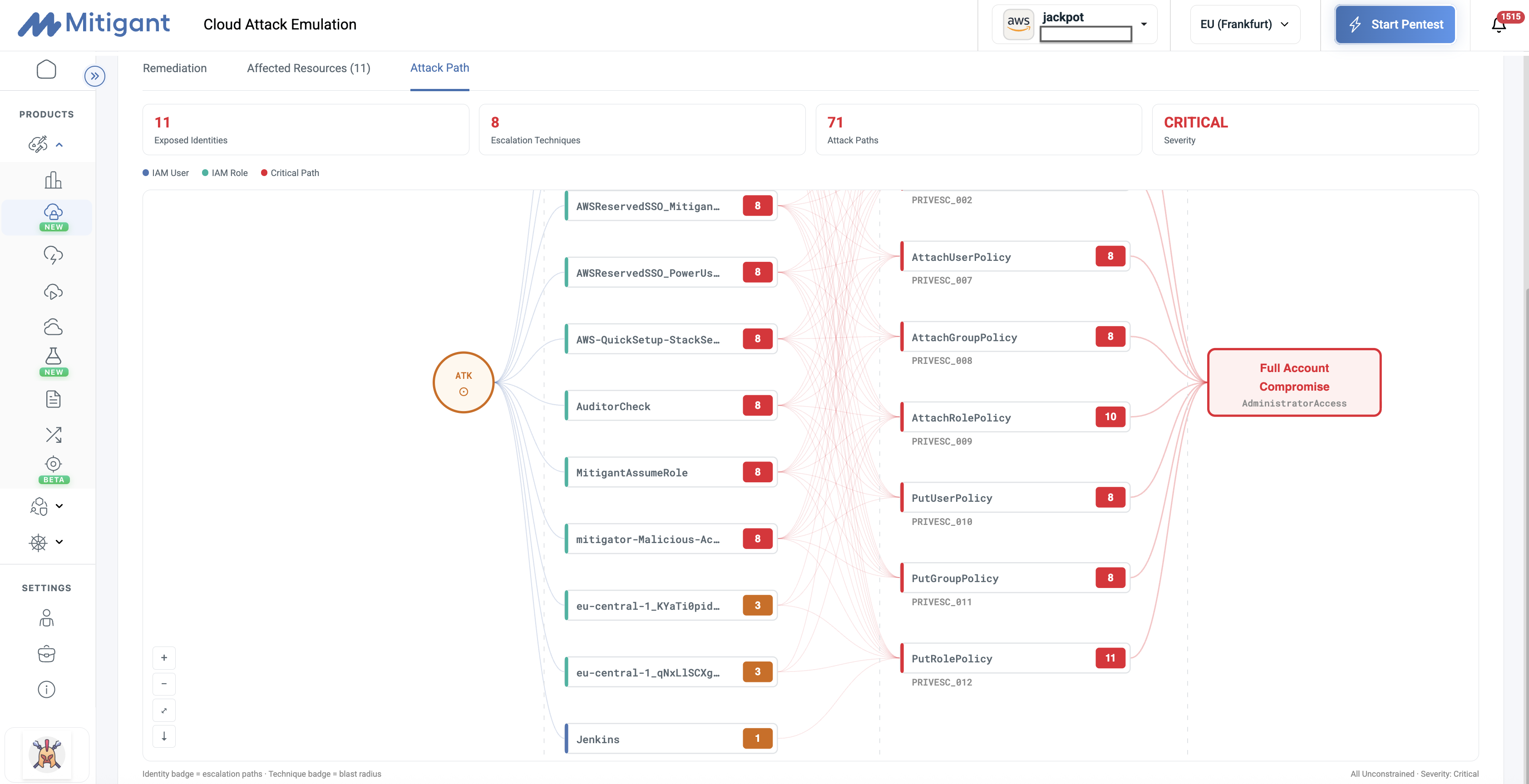
Attack Path Visualization
A list of technique IDs tells a security engineer what the vulnerability is. A graph tells them how far an attacker can go. Attack Path Visualization presents IAM escalation paths as an interactive directed graph, surfaced in the Attack Path tab within each pentest finding.
The graph renders identity nodes on the left, escalation technique nodes in the center mapped to PRIVESC IDs and MITRE ATT&CK references, and outcome nodes on the right showing the resulting access level. Multi-hop paths, where an attacker chains two or more techniques to reach a higher privilege level, are represented as branching edges through the graph. Seeing that a specific IAM user has a three-hop path to administrator access is more actionable than reading a list of API call names.
The graph is interactive: users can pan, zoom, fit the view, and download it as an SVG for inclusion in pentest reports or executive briefings.
What This Unlocks for Security Teams
MSSPs and security teams running Prowler or Wiz today can leverage these capabilities to address several operational gaps including:
Attack surface context, including internet-exposed resources. Posture findings alone do not tell you which misconfigurations are reachable from the internet. Mitigant includes internet-exposed resources in the pentest scope, so the findings that surface reflect real-world attacker access, not just internal configuration states.
Validated findings with a 5-minute MTTV. Manual triage of critical and high-severity findings from a CSPM report is time-consuming and imprecise. The Mitigant pentest workflow validates findings through passive and active attack execution, reducing thousands of posture findings to a focused, confirmed, evidence-backed set in approximately 5 minutes. The manual filtration step is replaced by automated exploitability analysis.
Fully automated execution, on demand. A pentest can be initiated at any time and produces a structured report without manual intervention. For teams running continuous security programs or firms delivering recurring engagements, this removes the scheduling and setup overhead from each test cycle.
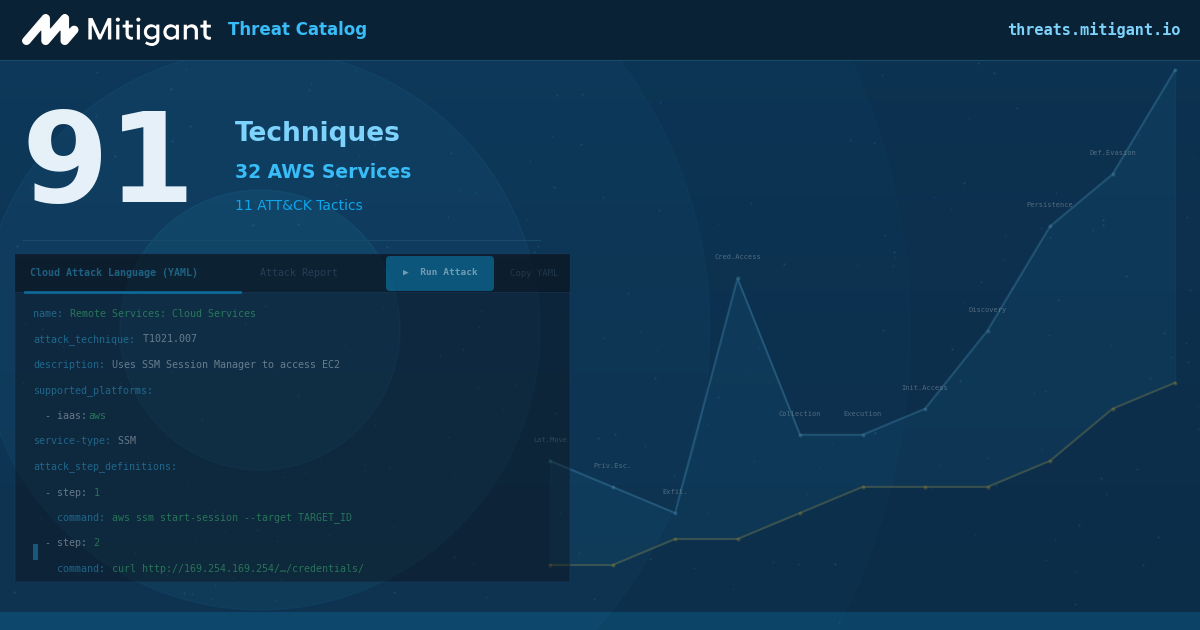
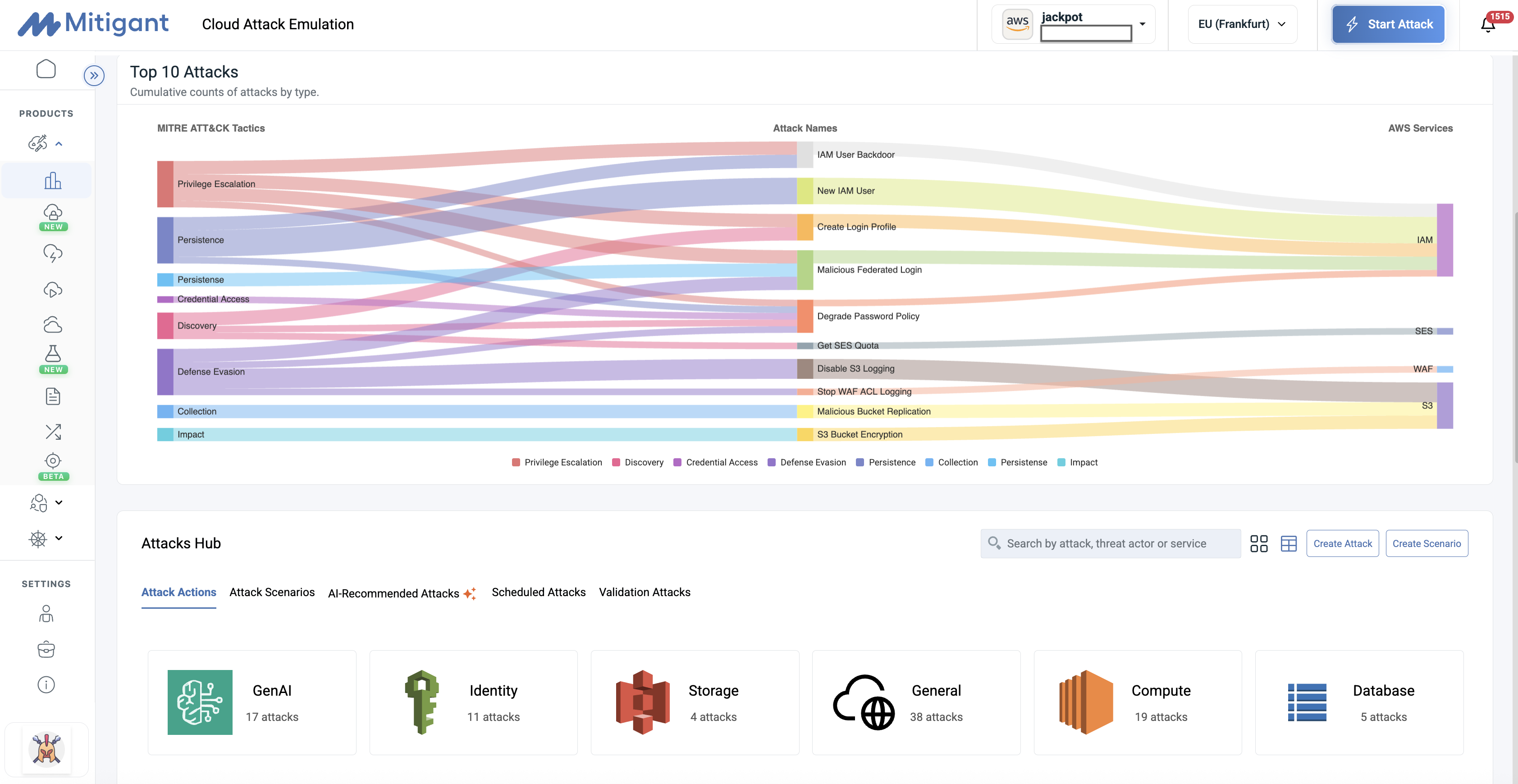
Over 300 attacks for further testing and exploitation. Beyond the initial posture-driven selection, Mitigant's catalog of over 300 cloud attacks is available for deeper testing and exploitation scenarios. Attack actions are atomic security tests targeting specific cloud services, each mapped to the MITRE ATT&CK framework. Attack scenarios chain multiple actions into realistic, multi-step campaigns. Together, they allow security teams to move well beyond the findings surfaced by CSPM into broader adversarial coverage across cloud services.
Contextual, SCP-aware privilege escalation. IAM escalation findings are evaluated within the SCP constraints of the AWS organization. Only paths that are genuinely executable under the organization's control policies are surfaced as findings. This eliminates false positives from evaluating IAM permissions in isolation and ensures remediation efforts are directed at real exposure.
What Is Coming Next
This release focuses on AWS. The next phase of the Privilege Escalation Engine will expand coverage to Azure and GCP, where escalation paths involve different primitives: managed identities, service principals, RBAC assignments, and workload federation. Microsoft's own Azure Threat Research Matrix will inform the technique catalog for those platforms.
Pentest scheduling is also on the roadmap, allowing security teams and pentest firms to run recurring pentests automatically without manual initiation, keeping posture validation continuous rather than point-in-time.
We are also continuing to expand attack emulation coverage across all three major cloud providers, and deeper integration between posture findings and attack execution remains the core focus of the roadmap.
To explore these features, log in to your Mitigant account and start a new pentest, or book a demo to see them in action.